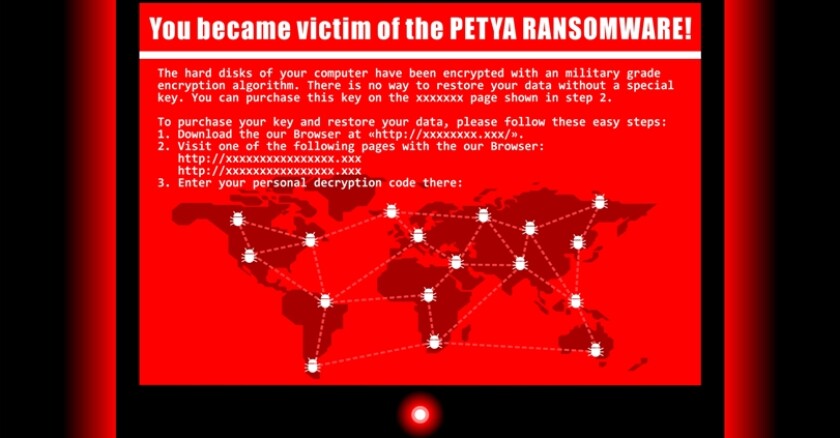
The most common name assigned to this cyberattack was Petya, although Trend Micro, Kaspersky Lab, Symantec and others pointed out that this is different than the Petya ransomware discovered in 2016.
Kaspersky even called the malware ‘NotPetya’ because they consider this to be a ‘sabotage attack’ or ‘wiper attack.’ More on those specific details below, but needless to say, this newest global cyberattack packed a huge punch that combined elements of multiple threat vectors.
The country of Ukraine was perhaps hardest hit (again), when Ukrainian banks, Kiev's Borispol airport, and energy firms Kyivenergo and Ukrenergo were brought down by this new cyberattack.
Wired magazine reported that the Petya ransomware epidemic may be a spillover from Cyberwar.
Kaspersky Lab announced on Friday that: “Banks, manufacturers, oil and gas utilities constitute roughly 82 percent of NotPetya's corporate victims ...
The findings further support the theory by a number of cyber-researchers that the attack's true intention was not to generate money via extortion payments, but rather to deal harm to key businesses, specifically those based in Ukraine.”
But different from the WannaCry ransomware that hit in May, significant impacts from Petya also hit hard in the United States, with reports of major outages that were still ongoing on July 1 in some major corporations nationwide. One example, includes Nuance Transcription services and radiology critical test results, which impacted hospitals in Texas and all across the country.
What Is This Malware?
So what exactly is this new malware that first appeared to be ransomware, but is clearly much, much more?
According to Tom Spring at Threatpost:
“The outbreak of the ExPetr (or Petya) malware isn’t a ransomware attack, but more precisely, it’s a wiper attack that sabotaged PCs globally, overwriting their Master Boot Record forever.”
“We actually consider this a sabotage attack or wiper attack. Whether it is intentional or not, I’ll leave that to others to speculate,” said Juan Andrés Guerrero-Saade, senior security researcher at Kaspersky Lab.
The Register.com (UK) offered everything you need to know about Petya, adding that this isn’t ransomware, it’s chaos.
"The superficial resemblance to Petya is only skin deep," noted computer security veteran The Grugq. "Although there is significant code sharing, the real Petya was a criminal enterprise for making money. This [latest malware] is definitely not designed to make money. This is designed to spread fast and cause damage, with a plausibly deniable cover of ransomware.”
To put it plainly, this code was built to destroy, not extort.
This YouTube video shows Petya, aka NotPetya, actually running on computers (as a demonstration).
Upon Further Review
Microsoft offered a blog on this new Petya ransomware that adds worm capabilities. They highlight most of the important details, such as delivery and installation mechanisms. “Microsoft now has evidence that a few active infections of the ransomware initially started from the legitimate MEDoc updater process.”
Also covered by Microsoft:
“Given this new ransomware’s added lateral movement capabilities it only takes a single infected machine to affect a network. The ransomware spreading functionality is composed of multiple methods responsible for:
- stealing credentials or re-using existing active sessions
- using file-shares to transfer the malicious file across machines on the same network
- using existing legitimate functionalities to execute the payload or abusing SMB vulnerabilities for unpatched machines
The new ransomware can also spread using an exploit for the Server Message Block (SMB) vulnerability CVE-2017-0144 (also known as EternalBlue), which was fixed in security update MS17-010 and was also exploited by WannaCrypt to spread to out-of-date machines. In addition, this ransomware also uses a second exploit for CVE-2017-0145 (also known as EternalRomance, and fixed by the same bulletin).
TheVerge.com speculated that this cyberattack was not launched by criminals but was a nation state attack against Ukraine. Still, there are definitely two conflicting viewpoints to the ransomware's origin.
All that evidence is still circumstantial, and there’s no hard link between yesterday’s attacks and any nation state. It could be Ukraine simply presented a soft target, and the attackers screwed up their payment and decryption systems out of simple carelessness. Functional or not, the software involved still has strong ties to traditional ransomware systems, and even if the attackers didn’t make much money off ransom payments, Petya was still collecting credentials and other data from infected machines, which could be valuable fodder for future attacks. That has led researchers like F-Secure’s Sean Sullivan to hold off on nation-state suspicions. “Maybe there’s multiple ways they’re working the money angle, but I think ultimately it’s about money,” Sullivan told me. “Tigers don’t change their stripes.”
If your organization has been infected, this article walks through some recommended action steps, although your options are somewhat limited.
Is There a Petya Link with WannaCry?
According to Firstpost.com in India, Petya was inspired by the attention received from the WannaCry cyberattack back in May.
However, Wired magazine proclaimed that the Petya hackers didn’t make WannaCry’s mistakes.
The NY Times offered this analysis from Nicholas Weaver, a researcher at the International Computer Science Institute and a lecturer at the University of California, Berkeley:
“Either it was a sophisticated actor who knew what they were doing — except screwed up horribly on the part where they actually get paid or it wasn’t about the ransom in the first place.”
The attack on Tuesday, like a similar assault in May called WannaCry, spread wider and faster than previous forms of known ransomware. But combined, they barely banked $100,000.
WannaCry spread by combining traditional ransomware with a worm, or a mechanism by which the attack could quickly grow. It was the first of its kind, said cybersecurity researchers, in that its goal appeared to be spreading as quickly as possible, rather than to successfully collect ransoms from victims.
Trend Micro offered (and answered) these FAQs regarding Petya. For example:
Is it a wiper or ransomware?
Answer: It’s both, actually. This threat manifests mainly as a ransomware given its tell-tale red flags: encryption and modification capabilities, ransom notes, and other related code artifacts.
On the other hand, this threat can also overwrite the affected system’s hard disk — and the modifications include wiping the disk. Another example of ransomware that modifies MBRs is HDDCryptor, the family that was used in anattack against the San Francisco Municipal Transport Agency.
Do Petya and WannaCry both use EternalBlue?
Answer: Yes. Both WannaCry and Petya exploit EternalBlue (MS17-010), a vulnerability in Windows’ Server Message Block, to infect endpoints and encrypt their files.
Where Is This Ransomware Trend Heading?
I agree with CNET that this global ransomware trend is just getting started — and is getting more dangerous.
Also keep in mind that different types of cyberattacks are now being merged to exploit vulnerabilities in more complex ways. Besides rendering a computer and its data useless, there is also a Trojan inside of Petya that steals victims' usernames and passwords.
Perhaps we should create a new hybrid malware category for Petya (or NotPetya) — calling it a ransomware-wiper?
Tech Republic encouraged readers to apply these six (fairly basic) tips to avoid ransomware after Petya and WannaCry:
- Perform strategic assessments of cyberthreats and vulnerabilities
- Rapidly spot and counter threats
- Develop business continuity plans
- Implement crisis and incident response planning
- Increase cyberhygiene policies and employee education
- Manage and patch vulnerabilities as soon as possible
Despite one "expert finding" that less than 1 percent of global Petya infections and impacts were felt in the USA, I heard constant reports throughout the past week of seriously impacted organizations all over North America. I suspect that some public- and private-sector organizations were not fully revealing the extent of their problems caused by Petya. WannaCry may have been more widespread, but the worldwide impact of Petya (so far) feels worse.
What is absolutely clear is that a scary trend is emerging regarding ransomware. More blended cyberattacks are coming that mix in elements of different threat vectors in new ways. Critical infrastructure providers need to be on special alert, and all organizations need to ensure their systems are patched to the greatest extent possible, given known Microsoft (and other software vendor) guidance.
The number of ransomware attacks has grown steadily over the past few years, from a coming-out party in 2013 to early hospital attacks last year to ransomware attacks on government this year to an under-reported incident of a South Korean hosting firm paying a $1 million ransom a few weeks ago.
In the last South Korean story, the company "found that both the internal backup ... and the external backup were infected with ransomware and all were encrypted." Also, several reports stated that the company negotiated the hackers down to (only) the $1 million ransom from an initial demand for over $4 million (US).
My fear is that the worst is yet to come. These global ransomware successes will embolden the bad guys and bring more copy-cat hackers.
While, unlike many others, I held off calling 2016 the year of ransomware, instead calling 2016 the year hackers stole the show with a cause (or the year of the hacktivist).
At the halfway point, 2017 is starting to look like the year of ransomware — with a destructive, wiper, (and who knows what's next) twist.