
As the landscape of cyberthreats grows, we look at some of the facts and figures behind what's affecting government. Click through for a glance at cybersecurity by the numbers.
To see the full infographic, click here.
[slideshow-break]

The “public administration” sector has the highest rate of email-born malware according to Symantec, with 1 in 120 emails containing malware. In 2017, that translates to each user averaging a little more than one email containing malware per week. Phishing attacks are more common, with users in public administration getting one per 38 emails received.
[slideshow-break]

States responding to the 2016 Deloitte-NASCIO Cybersecurity Study unanimously reported having an enterprise-level chief information security officer (CISO). In September 2017, Alaska joined their ranks with the appointment of the state’s first-ever CISO, Shannon Lawson.
Plus, according to the National Initiative for Cybersecurity Education, 285,000 cybersecurity positions went unfilled in 2017. Cyber Defense Magazine reports that by 2022, 1.8 million additional people will be needed to fill open jobs in cyber.
[slideshow-break]
According to Cisco, file formats from Microsoft, namely Word, PowerPoint and Excel are the most common malicious file extensions, representing 38 percent of the total. And Varonis finds that 21 percent of all files are not protected in any way.
[slideshow-break]
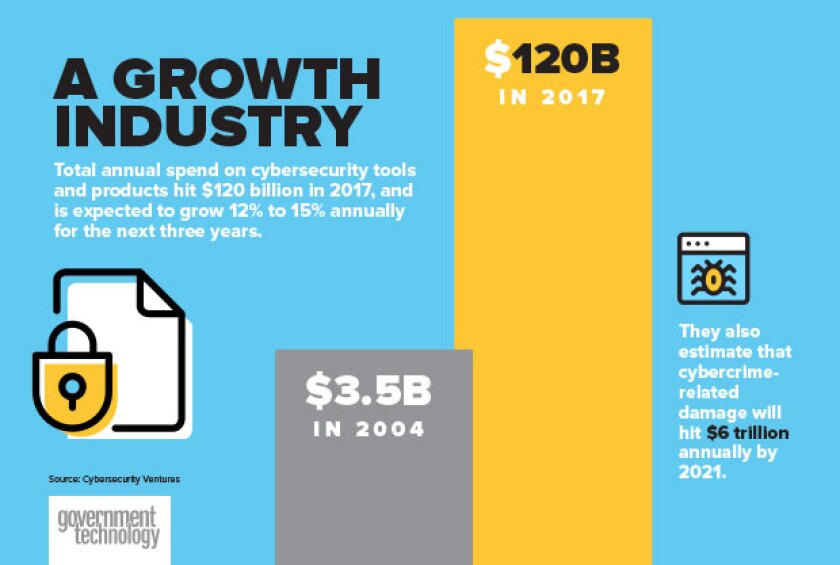
According to research firm Cybersecurity Ventures, in 2017, total spend on cybersecurity tools and products was $120 billion, up from $3.5 billion in 2004. An annual growth rate of 12 to 15 percent is expected for the next three years.
[slideshow-break]

[slideshow-break]

Further, Accenture finds that the costliest part of a cyberattack is information loss, which it pegs at 43 percent of the total cost. The average global cost of cybercrime increased by more than 27 percent in 2017.
[slideshow-break]

Breached
Confidential Base Info ExposedFitness app Strava made an effective case for its far-reaching user base in November 2017, putting out an interactive map that plotted 13 million data points showing how people used the app to work toward their health goals. But some of those users were active members of the military. In January, the Institute for United Conflict Analysis uncovered the fact that by putting out the map, Strava revealed the locations of U.S., Turkish and Russian military bases.
State Cybercenter Gets the Word Out
A jewelry company with a very high-profile retail partner, Walmart, failed to secure a set of customer data containing personally identifiable information, passwords and payment information, exposing data on 1.3 million customers. The exposure spanned several months in early 2018. First discovered by a security firm, the breach was broadly reported by the New Jersey Cybersecurity and Communications Integration Cell, the state’s threat-sharing network, aimed at protecting public, and private, organizations from cyberthreats.
Teacher Data Briefly Vulnerable
Education systems are rich targets for would-be data thieves, so thankfully the breach of the Pennsylvania Department of Education’s Teacher Information Management System lasted just 30 minutes one February afternoon. During the incident, blamed on employee error, the personal data of current and former teachers was exposed.
Voter Data Not Secret
An unidentified hacker obtained two databases that the Sacramento Bee (Calif.) had stored on third-party servers, demanding a bitcoin ransom to recover them. Along with personal information from more than 50,000 subscribers, the hack also included voter registration data from 19.4 million California voters: addresses, phone numbers and party affiliations, as well as places and dates of birth. The newspaper didn’t pay the ransom.
[slideshow-break]








